Automated Threat Response with SOAR
Earlier, there were very few options available to sneak into an organisation’s network. Today, the ways in which cyber criminals can get into an organisation has dramatically increased. There are multiple vulnerable platforms such as cloud data centers, mobile devices, file sharing platforms, IoT devices and many more that provide uncountable ways that compromise the network security.
Even in a well configured SIEM to detect these attacks, this can lead to alarm fatigue and slower Time to Respond (MTTR- Mean Time to Respond) as the response involves human intervention.
In order to ease the situation and decrease MTTR, most of the organizations are now turning to automated Response solutions that identifies threats and automates responses quickly.
Now, what is SOAR?
Security Orchestration, Automation and Response — often shortened to SOAR — creates a more modernized approach to analyse security information and data collection on security threats from multiple resources without human intervention for the detection of cyber-threats and to respond to the security events effectively. With the help of SOAR, time-consuming manual tasks are automated many times faster than the traditional cyber security approaches with more effective incident response.
Organizations with too many security incident alerts and a handful of analysts need to adopt a mechanism which empowers them to automatically respond to security alerts. It’s no question that, response time to the alert immensely contributes to effective cyber security. Nowadays, more security teams are automating their processes to get the speed they need for business. Gone are the days when speed was the hour, now it is certainly the need of the seconds.
Benefits of Implementing SOAR Technology
SOAR is the best solution for analysts stuck in the maze of alerts and one of the best guide for the analysts who focus solely on investigating and responding to events on their whole day. Treating an unending stream of alerts can limit Security Operations Centre (SOC) from reacting quickly and effectively. SOAR enriches the events to prevent false positive alerts from lowering the sensitivity bar. Organisations that adopts Security Orchestration and Automation (SOAR) are now enjoying its benefits of enhanced speed, ease of operation and reduced the human error.
SOAR security solutions can improve critical cybersecurity operations such as incident response, threat detection, security reports etc. by helping the analysts, especially those who are part of a SOC team, to manage their company’s overall security approach in a better way. SOAR provides a quick and accurate way to process large volumes of incident alerts and log data. SOAR combines different technologies and connecting security tools to glue them for working together and participating in incident response.
Consider an instance where a company gets thousands of malicious emails every day. Is it possible to investigate each reported email manually? This is where SOAR come into place. For each malicious email, this response tool orchestrates each step to the response mostly without any human intervention. Based on the value of the results, analysts can be notified and enter into the process. On this actual case, we can see security orchestration playbook can react to the incident and implement suitable remediation.
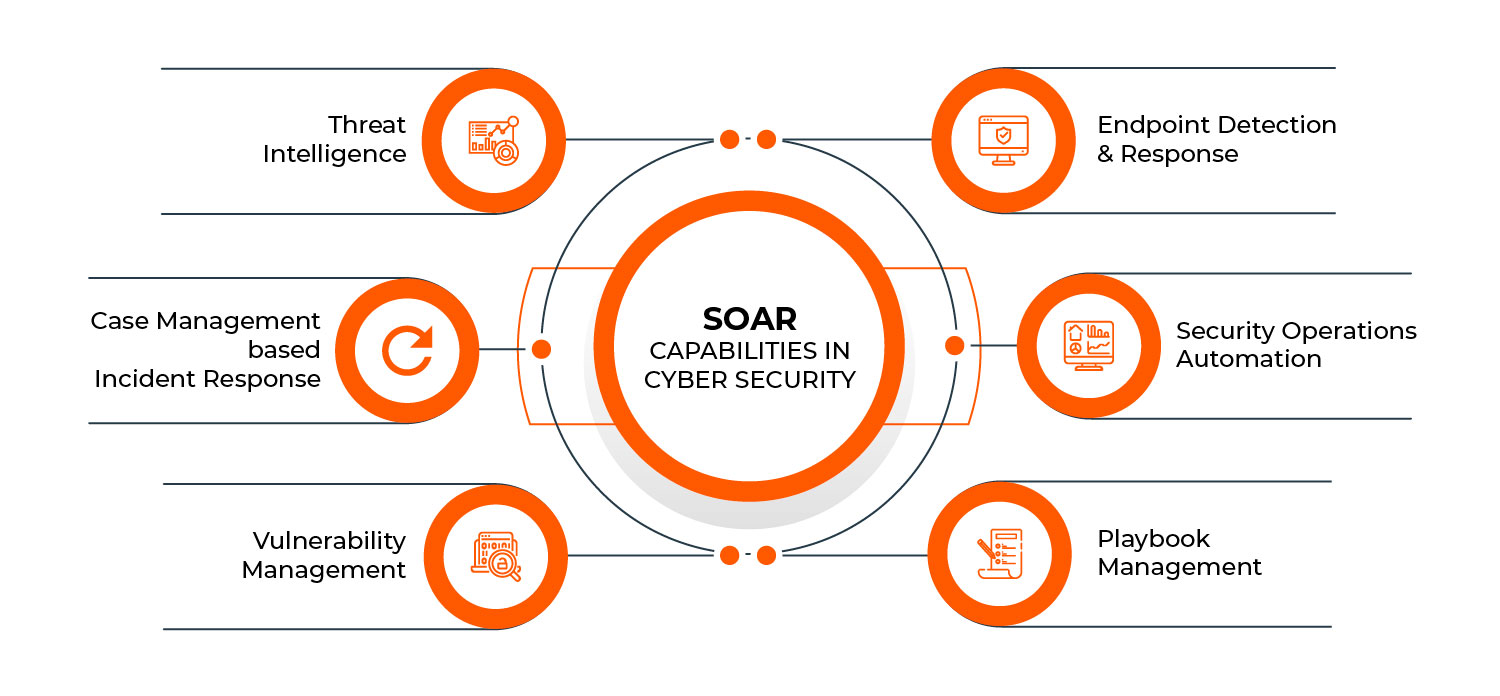
SOAR Capabilities in Cybersecurity:
- Threat Intelligence
- Case Management based Incident Response
- Vulnerability Management
- Endpoint Detection and Response
- Security Operations Automation
- Playbook Management
SOAR Use Cases:
Below are the few of the use cases which can be implemented with the advent of SOAR solutions for effectively mitigating cyber threats:
- Automating malware analysis
- Automating threat-hunting
- Endpoint Diagnostics
- Automating Failed User Logins
- Automating IOC enrichment
- Automating VPN checks
- Automating vulnerability management
- Automate incident severity assignment
- Responding to phishing attacks
- Endpoint Diagnostics
What is SOAR in relation to SIEM?
Security Information & Event Management (SIEM) refers to the tools and technologies for effectively gathering and storing security data. SIEM aggregates and correlates all of this gathered data by further identifying and analysing it. SIEM solutions tend to produce many alerts and may increase the workload for SOC analysts. Each alert must be reviewed and investigated by an analyst to determine if the event is a false positive, or an actual incident which requires further investigation and remediation, being a tedious process.
This is where the SOAR solution comes into play and can be used effectively in conjunction with a SIEM tool. While the SIEM detects the potential security incidents and triggers the alerts, the SOAR solution takes these alerts to the next level, triaging the alert, automatically investigating, responding to them by taking remediation steps wherever necessary, thus reducing manual interventions.
We can use SOAR to augment the capabilities of SIEM hence increasing the efficiency of SOC. Integrating a SIEM tool with a SOAR solution combines the power of each to create a more efficient and responsive security program. Taking the advantage of the SIEMs ability to ingest bulk data and to generate the alerts, the SOAR solution can then be layered on top of the SIEM to manage the incident response process to every alert, automating and orchestrating the repetitive tasks which would otherwise take many human analyst hours to complete.
How SOAR can improve SOC efficiency?
1. Minimize Human Intervention:
The SOAR platform will incorporate the repetitive routine tasks into playbooks that lay out the end-to-end incident response steps. Hence SOAR helps SOC analysts with everyday constant tasks and includes them in an overall process of how to handle any given incident.
It is difficult for the incident response team to deal with critical incident, data exfiltration etc. SOAR can automatically respond to threats and reduces the response time to seconds, so attackers have less system access time.
2. Cost Reduction:
A SOAR solution reduces the amount of work in SOC that needs to be done manually, increasing efficiency and performance. By taking advantage of the efficiency and productivity to reduce some of the security-related operational costs.
For example, SOAR helps in optimizing and decreasing an analyst’s workload by automating repetitive everyday manual duties and saving their time to spend more on research and investigation of threats. Hence decrease an organization’s expense in manpower accordingly.
3. Comprehensive Integration:
The main benefits of SOAR systems for organizations is that they can provide integration with SIEM tools, Reputation checkers, ticketing tools, firewalls, intrusion detection systems, and threat intelligence platforms etc. This saves time since analysts need not have to collect information from different tools and find out how to connect it into a valuable, actionable summary.
4. Streamlined Operations
SOAR solutions create pre-built security playbooks that guide users through investigation workflows. Users can rely on the SOAR software solutions and integrate them into the security frameworks, without knowing about which parts should be automated.
SOAR solutions prioritize threats automatically so it can help less-experienced analysts to choose which incidents they should address first. SOAR solutions also has the ability to automatically investigate low priority alerts can find out the false-positive ones, which may not require immediate response.
By automating the handling of these alerts, analysts can dedicate most of their time and attention to situations where human intervention really is required while the SOAR solution handles the rest.
Achieving maximum results with minimum resources may sound impossible, if you are doing it manually. But practically speaking, it can be possible with SOAR security tools.