You might have heard of the North Sentinel Island in the middle of Bay of Bengal that hosts the most isolated tribe in the world. Despite several attempts to break in or contact the island, it was always defended violently by the natives and the island still remains untouched. It is considered to be one of the most secured places on planet earth guarded both by the local tribes and the government. When it came to naming the most powerful weapon in Azure cloud security arsenal, Microsoft have chosen the right name for it- Azure Sentinel.
As we see, organizations are racing to move their network architecture to cloud platforms due to a plethora of advantages it has relative to On-Prem data centers. Gartner has predicted a prodigious 17 percentage growth in cloud market by 2020 that accounts to around $266.4 billion. Within all cloud platforms Azure is the preferred choice for most due to its seamless integration to Microsoft AD Infrastructure. As the cloud environment grows, the security landscape also changed drastically. That brings us the question, are the legacy SIEM platforms capable enough to cope with the new attack vectors and protect them?
What’s Azure sentinel under the hood?
Azure natively provides a variety of features when it comes to data analysis and security, that includes by not limited to
- Azure Log Analytics Workspace and Azure Monitor for Collecting, Storing and analyzing log, Metrics and Telemetry data
- KQL(Kusto Query Language) to query and Interact with data
- Azure Logic Apps for running Logic workflows helps to schedule, orchestrate and automate tasks
- Azure Machine learning Studio for advanced supervised and unsupervised machine learning
- Azure Fusion for multistage attack detection
- Azure Workbooks for Visualization
- Many security features like Azure Security Center, DDOS protection, Advanced Threat protection, etc.
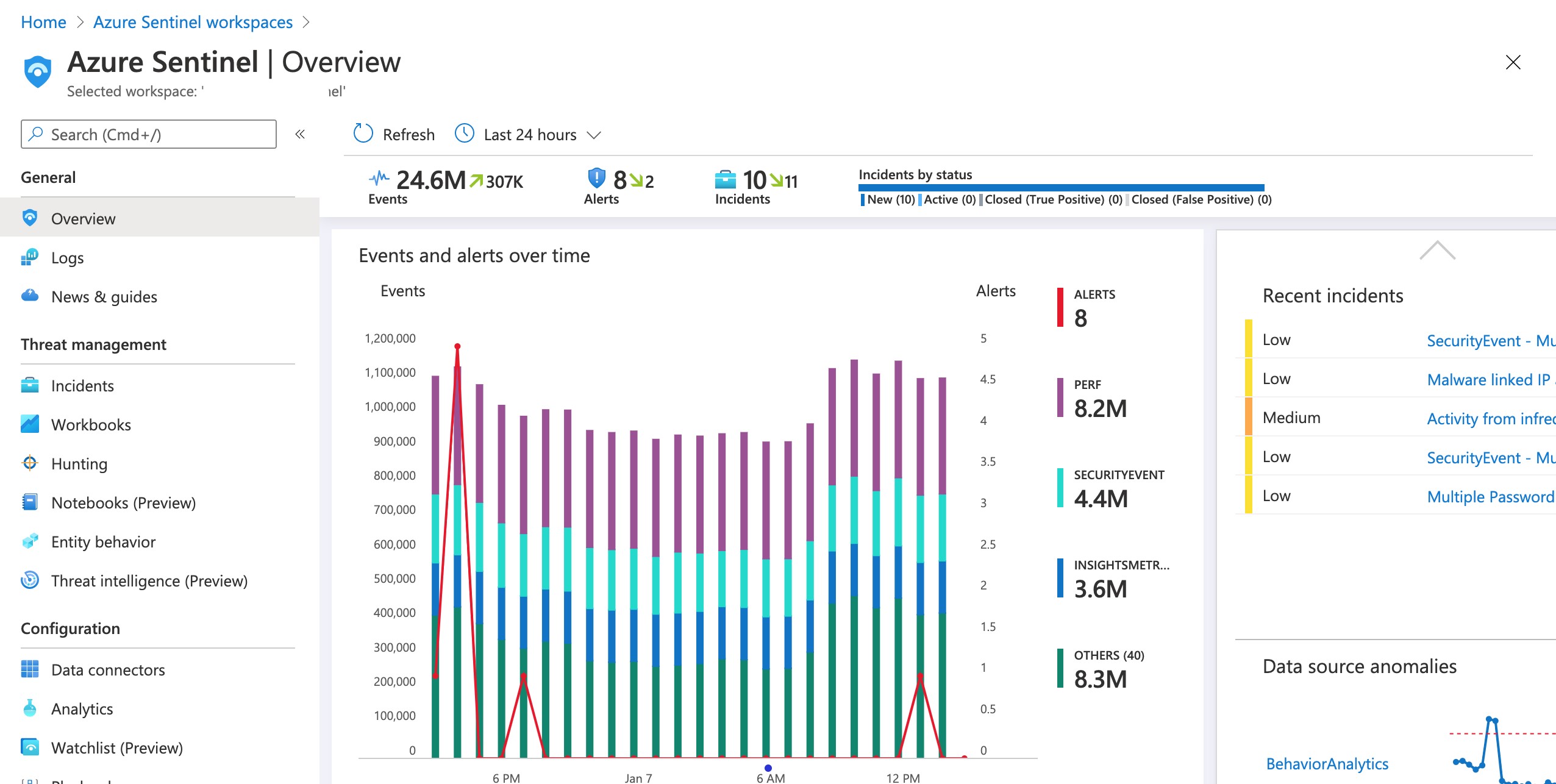
Azure sentinel integrates all the above features under one blanket and provide the benefits of all the features right from one tool. Integrating all these features in to one UI makes it easier to manage, analyze and respond to threats.
Azure Sentinel Features
Let’s take a ride through the various features Sentinel provides in order to make it the newfound favorite in Security market. We will analyze the following Standard SIEM features provided by sentinel based on their availability and complexity.
- Cost of Onboarding
- Ease of deployment
- Data Collection and Processing
- Data Analysis
- Threat Intelligence
- Machin Learning
- User and Entity Behavior analysis
- Dashboards
- Reporting
Cost of Onboarding
Microsoft started referring itself as the largest security provider in the world lately than a software and infrastructure development company. We have to agree with the fact that the latest enhancements what its delivered in security marketplace proves the claim to be right. Microsoft has tried to invest decades of experience in to Azure sentinel to make it a near perfect SIEM solution, that can belittle any other enterprise SIEM solutions, at the same time making it affordable with competitive pricing models.
Azure provides two pricing models for Sentinel:
Pay As You Go: With Pay as you go model, you pay for how much data ingested, roughly USD 2.64 per GB Ingested. This option would be good for small organizations that generate only few GBs of data a day. Note: There are other costs applicable for different services within Sentinel arsenal like Data Retention more than 90 days.
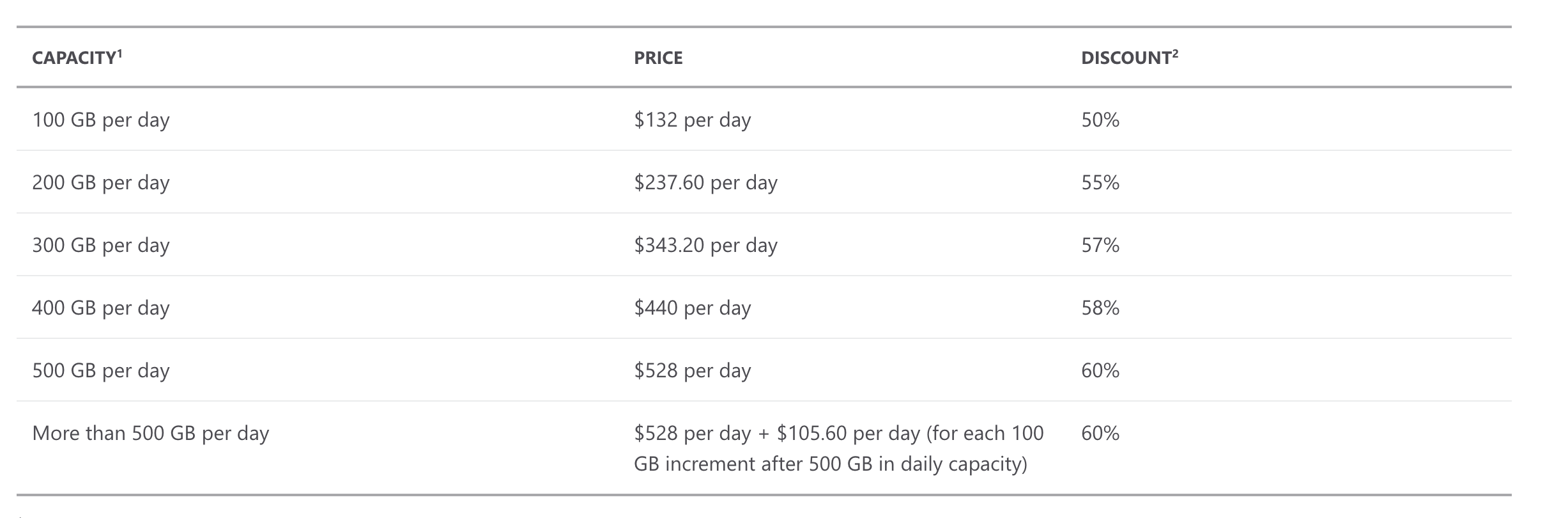
Capacity Reservation: If you are a larger organization that churns out hundreds of GBs of data every day, Azure gives discounted pricing with Capacity reservation. It offers up to 60% discount comparing with Pay-As-You-Go pricing as the capacity increases.
Free Trail: Azure provides a free 30-day trial for Proof-of-Concept purposes.
Ease of deployment:
When it comes to On-Prem SIEM Solutions, Deploying the solution to the network itself is a complex process that includes procuring and Provisioning hardware or VM, installing the host OS and necessary application, Licensing, setting up the networking, etc. Sentinel being a SaaS platform, deploying it is as easy as few clicks and couple of minutes of waiting for the solution to be deployed ready to use.
This post is written by Ranjith Kesavan, Sr. Cyber Security Lead (SOC Operations and Blue Team) at DTS Solution