Reading security logs requires a higher level of permission that other logs. Below are the steps to configure the right permissions for reading security logs.
Configuring permissions to allow reading security logs
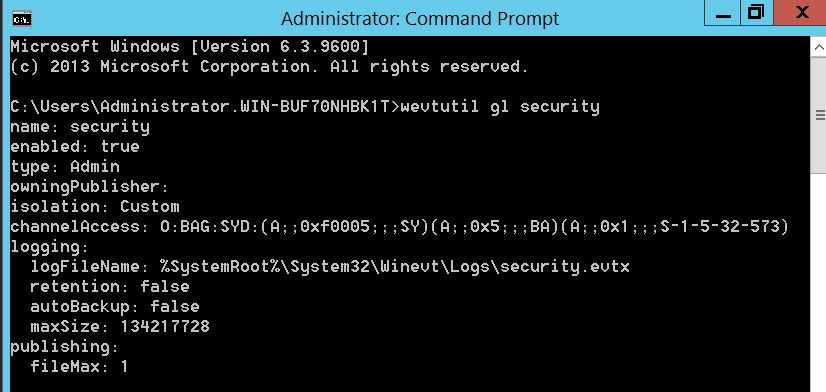
- Create a security string for access to security logs. Run the command wevutil gl security from cmd.
- Copy the string from the channelAccess line that starts with O:BAG:SYD: and append it with the following string: (A;;0x1;;;NS)
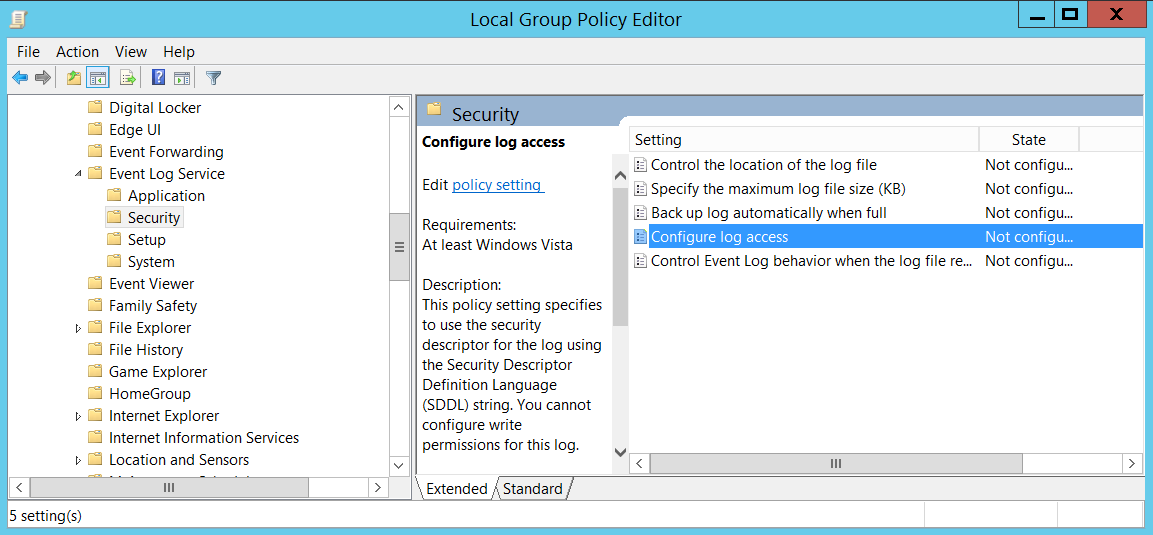
- From the Group Policy Management Editor, navigate to Computer Configuration>Policies>Admin Templates>Windows Components>Event Log Service>Security> Configure log access
- Right click on ‘Configure log access’ and click edit
- Click on “enabled”
- In the “Log Access” text box, enter the string created by appending to the wevutil command output.
- Click Ok
Configuring Windows Event Forwarding
First, we enable the Windows Event Collector service.
- Open the ‘Run’ prompt by pressing the Windows Key + R.
- Type in ‘services.msc’ and click ‘OK’
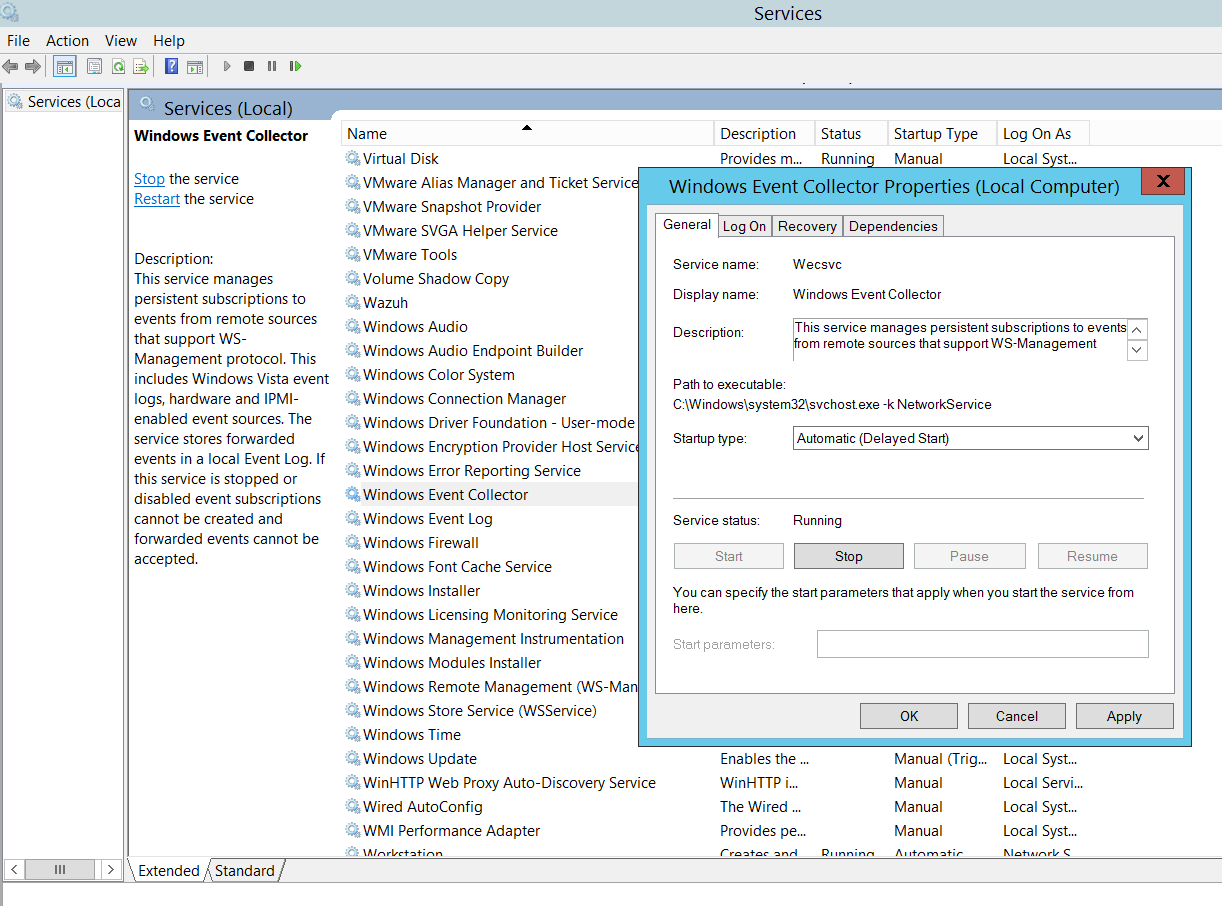
- In the ‘Services’ window, scroll down to ‘Windows Event Collector’, right click and select ‘Properties’.
- Change the ‘Startup Type’ to Automatic (Delayed Start) and click the ‘Start’ button.
- Click ‘OK’
The next step is to create a ‘Subscription’ in the ‘Event Viewer’
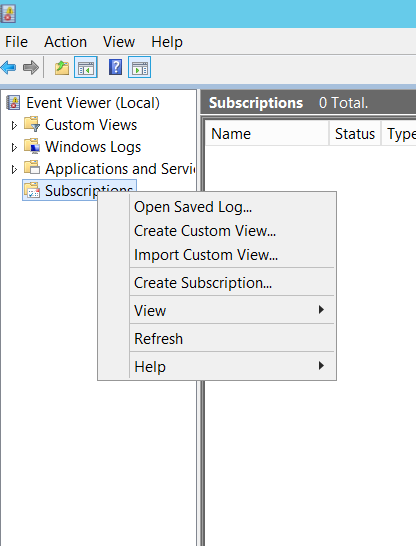
- Open the run prompt again, type in ‘eventvwr’, and click ‘OK’. This opens the Event Viewer window.
- In the Event Viewer window, right click on ‘Subscriptions’ and select ‘Create Subscription’.
- Give the subscription a name and select the ‘Source Computer Initiated’ radio button.
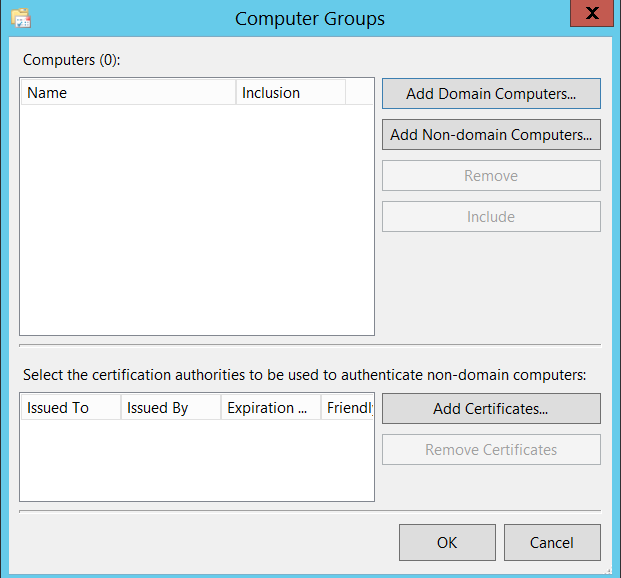
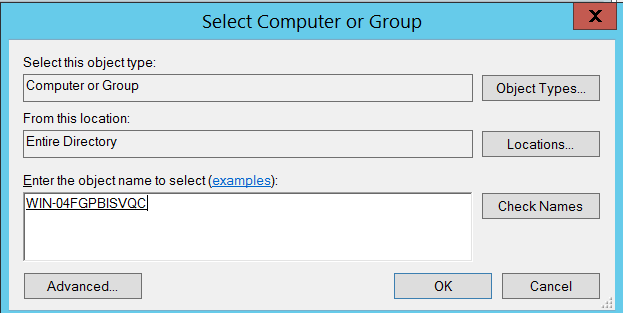
- Click ‘Select Computer Groups’ and select ‘Add Domain Computers’.
- In the ‘Enter the object name to select’ text box, enter the computer name and click ‘Check Names’. Once the correct computer name is populated, click ‘OK’.
- This (unfortunately) needs to be repeated for each computer name from which events are to be forwarded.
- In the ‘Subscription Properties’ dialog box, click ‘Select Events’. This opens the ‘Query Filter’ dialog box.
- In the ‘Query Filter’ dialog box, select the Event Level and Event Log options as appropriate.
- Click ‘OK’ on the ‘Query Filter’ and ‘Subscription Properties’ dialog boxes.
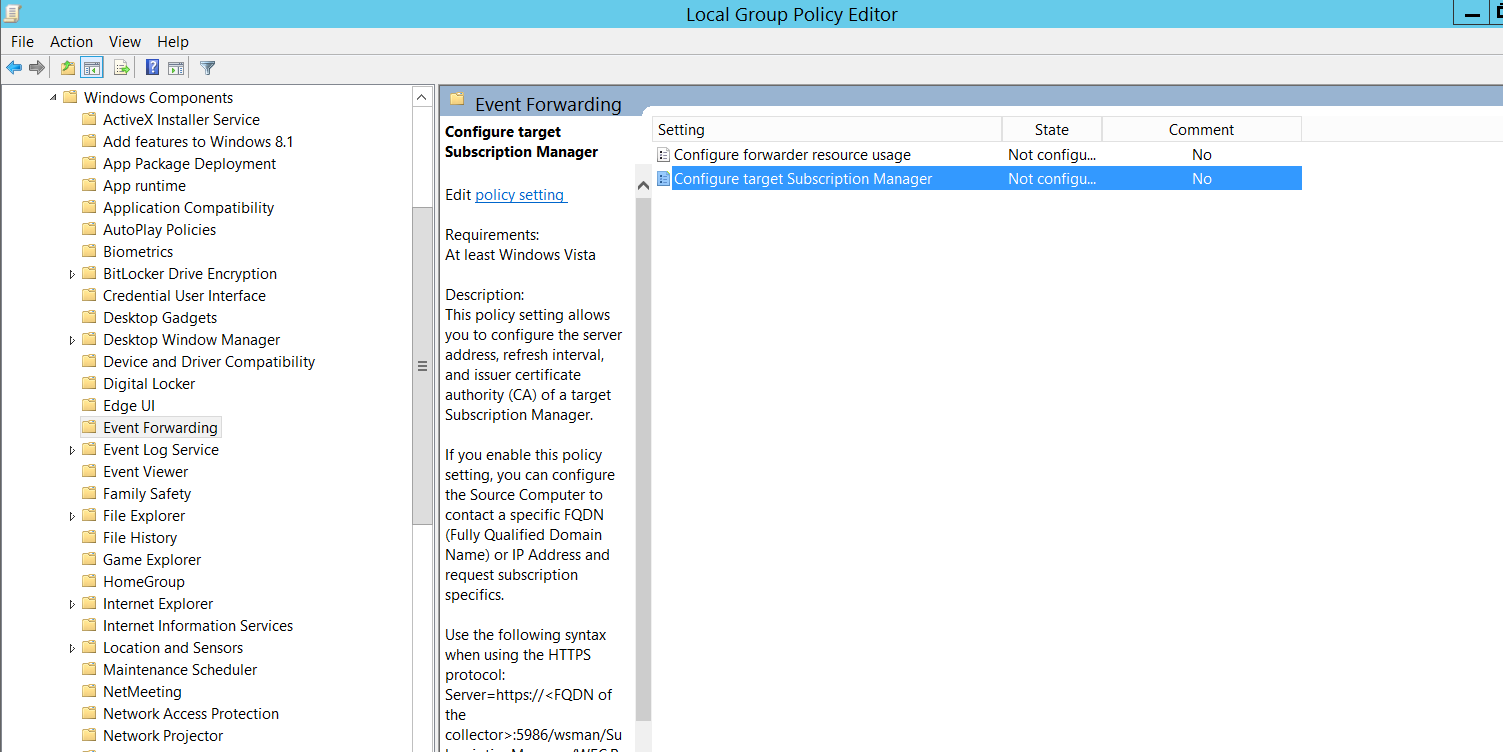
The next step is to configure the WEF subscription server from Group Policy.
- Open the Group Policy editor again. This can be done from Control Panel as discussed earlier or by typing ‘gpedit.msc’ into the ‘Run’ prompt.
- From the Group Policy Management Editor, navigate to Computer Configuration > Policies > Administrative Templates > Windows Components > Event Forwarding > Configure Target Subscription Manager
- Right click ‘Configure Target Subscription Manager’ and click ‘Edit’.
- Change the radio button to enabled.
- Under ‘Options’, click ‘Show’ and fill in the value in the below syntax.
Server=
- Click ‘OK’ on ‘Show Contents’ and ‘Configure target Subscription Manager’ dialogs.
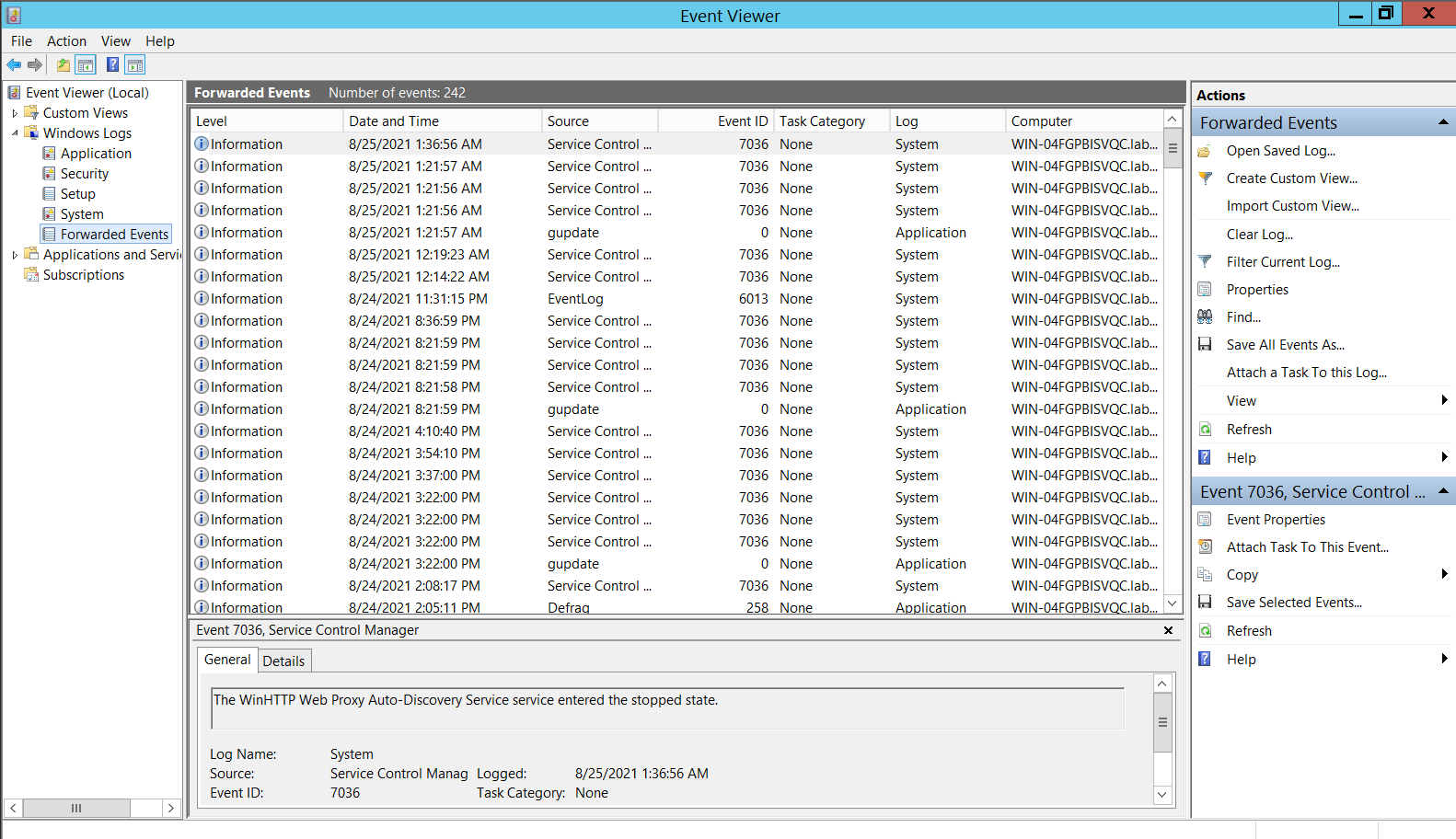
Verifying that Event Forwarding is working
- Open Event Viewer as discussed earlier in the article.
- Click on Windows Logs > Forwarded Events
- The forwarded events should be populated as below
This post is written by Sandeep Renjith, Cyber Security Analyst at DTS Solution