LSASS Dumping Techniques

Local Security Authority Subsystem Service (LSASS) is the process on Microsoft Windows that handles all user authentication, password changes, creation of access tokens, and enforcement of security policies. It stores multiple forms of hashed passwords and even stores plaintext user passwords in some instances. LSASS is a fruitful target for adversaries because it contains valuable data like encrypted passwords, NT hashes, LM hashes, and Kerberos tickets which can be used for privilege escalation, data theft, and lateral movement
LSASS Dumping
Adversaries may attempt to access credential material stored in the process memory of the Local Security Authority Subsystem Service (LSASS). The system generates and stores a variety of credential materials in LSASS process memory after a user logs on successfully. By default, LSASS stores credentials associated with logon sessions since the last restart, which have not been closed (logged off). This means that once a user is logged off, LSASS may clear the credentials after a certain period of time, which varies by the operating system and security settings. As well as in-memory techniques, the LSASS process memory can be dumped from the target host and analyzed on a local system. LSASS dumping can be done broadly by two techniques native processes and custom adversary tools.
LSASS Dumping Techniques
Now that we have covered ways to process LSASS memory dump files, here are some ways to actually create those dump files from Windows machines.
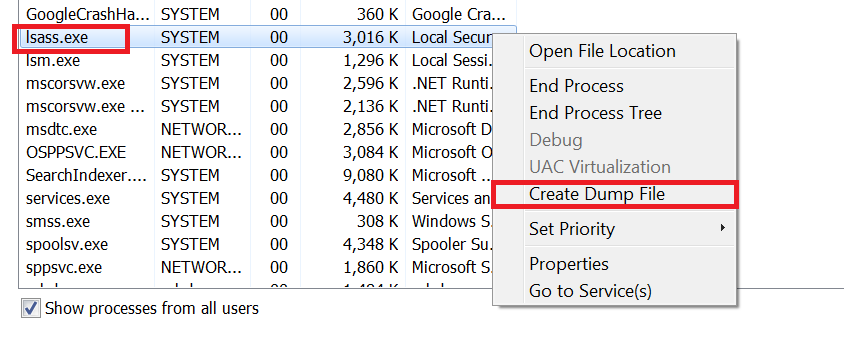
Task Manager:
Task manager is a very reliable option as Windows Defender does not alert on this by default. The downside to this method is it does not scale well and is relatively slow. Task Manager is capable of dumping arbitrary process memory if executed under a privileged user account. It’s as simple as right-clicking on the LSASS process and hitting “Create Dump File.” as shown in fig below.
Procdump
Procdump is a Windows SysInternals tool that can be used to create memory dumps of processes. Just like task manager this method is also slow and doesn’t scale too well and above that adversary will need to install procdump in the target machine. The procdump command for creating a memory dump of LSASS is:
procdump.exe -accepteula -ma lsass.exe lsass.dmp
Crackmapexec:
Crackmapexec is an excellent tool to remotely perform a dump of LSASS. It scales really well as an adversary can simply point and shoot at a whole subnet or list of IP addresses with credentials that have local admin access. The command for creating a memory dump of LSASS on a remote machine is:
crackmapexec smb -u -p –lsa
Mimikatz:
Mimikatz is the best-known way of dumping LSASS. It has the ability to access LSASS credential material, Kerberos tickets, create tokens, pass-the-hash, and more. This toolset is open-source and can readily be downloaded from the GitHub repository. Mimikatz requires local administrator rights to the host on which it will be used. This is because it has to assume “Debug” privileges as it uses Windows debugging functionality to access the LSASS memory space.

As seen in the figure above, Mimikatz will attempt to pull credential material from multiple sources, including MSV, TSPKG, WDIGEST, KERBEROS, SSP, and CREDMAN.
LSASSY:
Lsassy (7) is an interesting tool that uses a combination of the above methods to remotely dump LSASS. The default command attempts to use the comsvcs.dll method to dump LSASS via WMI or a remote scheduled task. The command for creating a memory dump of LSASS using LSASSY is:
lsassy -d test.lab -u -p
Mitigation Techniques
- Decommission all end-of-life Windows operating systems if possible.
- Restrict local administrative access as much as possible (M1026).
- Disable WDigest on all Windows operating systems prior to Windows 8 and Windows Server 2012 R2 (M1028).
- Enable Windows Defender Credential Guard (M1043).
- Monitor for registry changes to ensure WDigest is not reenabled and that Windows Defender Credential Guard is not disabled.
- Alert on and restrict pass-the-hash if possible.
- Enable Attack Surface Reduction (ASR) rules to secure LSASS and prevent credential stealing (M1040).
Detection Techniques
Command Monitoring:
Monitor executed commands and arguments that may attempt to access credential material stored in the process memory of the Local Security Authority Subsystem Service (LSASS). EDR, Sysmon Event ID 1, and Windows Event ID 4688 should collect relevant telemetry.
Process Monitoring:
Monitor for API calls that may attempt to access credential material stored in the process memory of the Local Security Authority Subsystem Service (LSASS). Also, Monitor for unexpected processes interacting with LSASS.exe. EDR, Sysmon Event IDs 1 and 10, and Windows Event ID 4688 should collect relevant telemetry.