Freeze – A Payload Toolkit for Bypassing EDRs using Suspended Processes
June 21, 2023
Freeze is a potent tool that makes it possible to build payloads that stealthily run shellcode and get beyond EDR security measures. Freeze removes Userland EDR hooks via various methods, and shellcode is executed in a way that evades detection by other endpoint monitoring tools.
Overview
EDR solutions can monitor the execution flow of a process, gather data for behavior-based analytics, and spot suspicious and malicious activities by modifying an application’s behavior through hooking. With this feature, post-initial compromise tactics (like code execution) and post-exploitation techniques (such as privilege escalation, lateral movement, or ransomware activity) may be detected more accurately. Freeze employs a method to start a process, then put it in the background. This strategy aids in hiding the process and keeps it from being picked up by any EDR software.Userland Hooks
The majority of products employ userland hooks to identify and stop harmful behavior, which is a systemic reason why EDR unhooking is such a common practice. Userland offers the broadest range of features that a security product may connect to, as well as a wealth of comprehensive telemetry that allows companies to infer behavior from the processes they are monitoring. Userland hooking’s drawback is that every component has the same privileges because they are all located at the same address. As a result, the hooks in a security product and the code of an adversary both have read and write access. The product can be tampered with if an adversary knows where a hook is and modifies or replaces it. This design has been tough for EDRs since it requires rewriting the entire product and might cause stability problems to move hooking to another part of a process, such as the Kernel. Over the past several years, some products have evolved by attempting to detect known adversarial tampering or overwriting hooks before these acts take place.Working of EDR Unhooking
Creation of suspended process: Before any EDR DLLs are loaded, Ntdll.dll is the initial DLL that is loaded when a process starts. This indicates that there is some time spent loading an EDR before it can begin hooking into and changing the assembly of system DLLs. Ntdll.dll is the only DLL that is loaded when a process is created in a suspended state. Additionally, no EDR DLLs are loaded, which indicates that the syscalls in Ntdll.dll remain unmodified. ASLR (Address Space Layout Randomization): A mechanism is needed to programmatically locate and read the memory of the clean suspended process so that it can be used to unhook the Freeze loader. Address space layout randomization (ASLR) is useful in this situation. An ASLR security method guards against vulnerabilities caused by stack memory corruption. To guarantee that every memory-mapped item, the stack, the heap, and the executable program itself are distinct, ASLR randomizes the address space inside a process. This is where things get interesting because while ASLR functions for position-dependent code, such as DLLs, it does not. The address space of DLLs, more especially known as system DLLs, is randomly generated once at the time of startup. Freeze gets this information from its own process without ever having to enumerate the suspended process because every DLL’s address is in the same location on every boot. The Freeze generated payload programmatically gets a copy of the .text section of Ntdll.dll (instead of entirely reading the DLL file) to overwrite the existing hooked .text section prior to executing the shellcode by finding the base address of Ntdll.dll and the offset of .text. Without using any of the memory modification API calls, Freeze utilizes the WriteProcessMemory function to overwrite memory regions that cannot be written to. WriteProcessMemory temporarily changes the permissions of the region of memory to be writeable when it is called to write to a portion of memory that is not configured to be writable. Without using the VirtualProtect function, it writes the value and resets the permissions; instead, it automatically uses the related Syscall (NtProtectVirtualMemory). ETW Patching: ETW produces this telemetry using built-in syscalls. Security products do not need to “hook” the ETW syscalls in order to access the data because ETW is also a natural capability that is included into Windows. As a result, Freeze patches multiple ETW syscalls in order to stop ETW, clearing the registers and shifting the execution flow to the following instruction. All loaders now by default patch ETW. Shellcode: Since only Ntdll.dll was recovered, Ntdll.dll is where all subsequent calls to execute shellcode should be made. We can define and call the NT syscalls required to allocate, write, and protect the shellcode using Go, effectively skipping the standard calls that are found in kernel32d.dll and Kernelbase.dll because these may still be hooked.Usage of Freeze
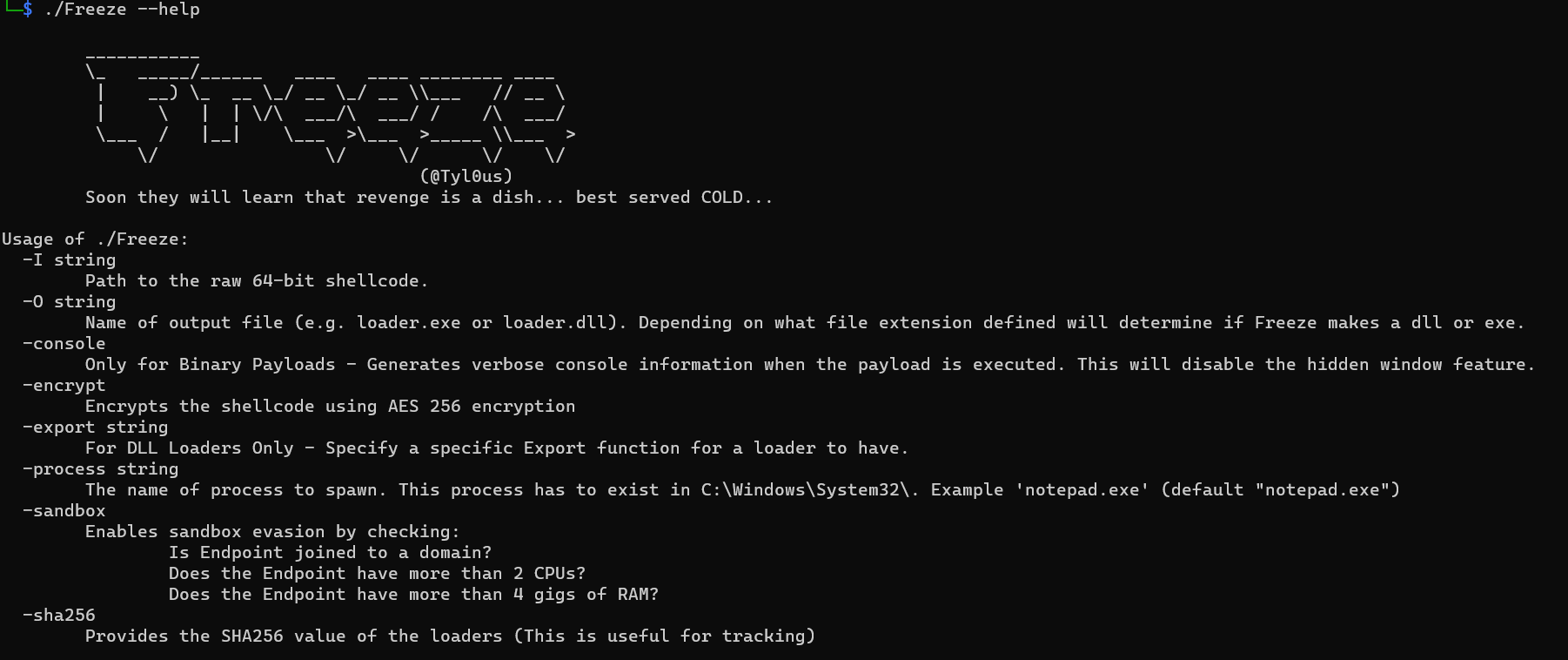
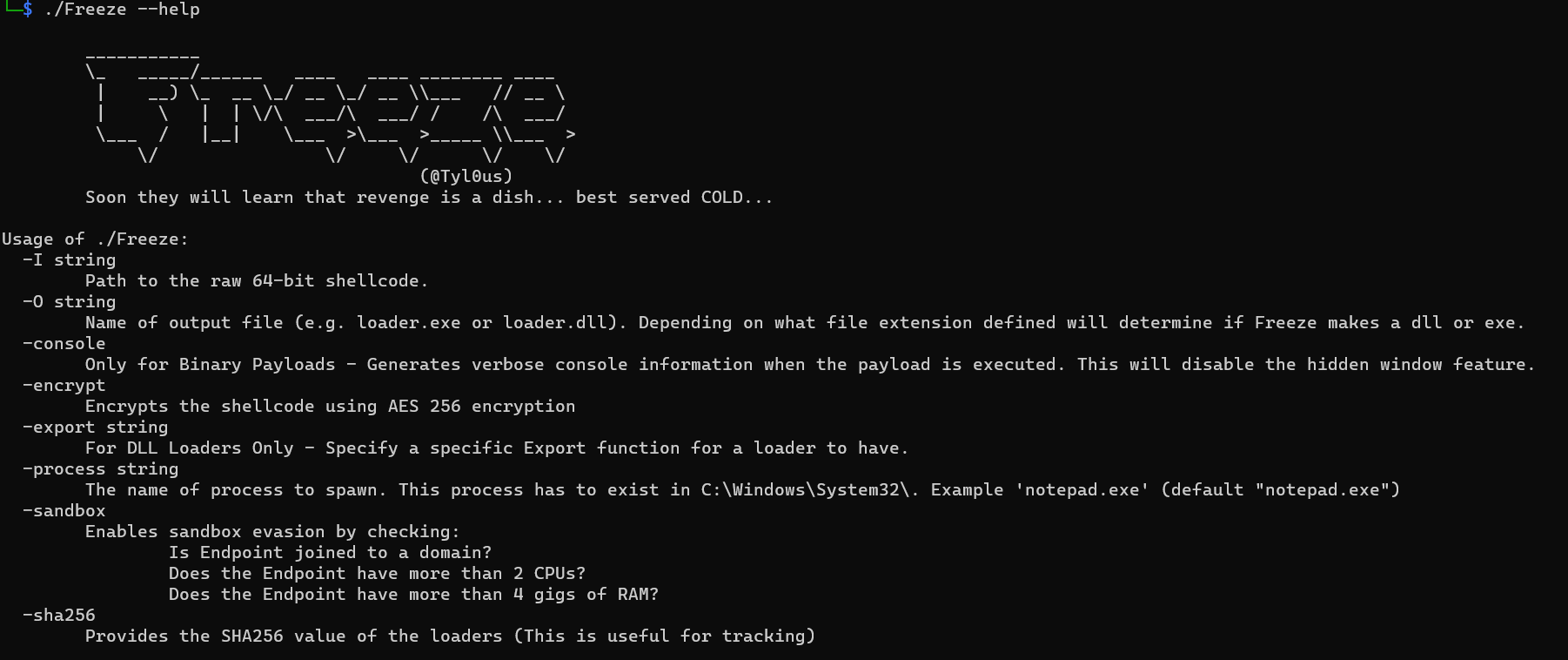
Freeze was developed in Golang by Optiv and is available at https://github.com/optiv/Freeze. Either an.exe or.dll file can be generated by Freeze. Make sure the -O command line option ends with either a.exe for binaries or a.dll for dlls in order to indicate this.